The Cost of Ignoring Data Security Management And How to Get It Right
Data security management is no longer optional for modern organizations; it is foundational. Businesses of every size are collecting and storing more sensitive information than ever. At the same time, cybercriminals are becoming faster and more sophisticated. Without a formal approach to managed data security, organizations leave themselves exposed to breaches, regulatory fines, and irreversible reputational damage.
Many companies turn to managed security services to supplement internal teams. However, building your own program from the ground up is just as critical. The numbers tell a stark story. According to a recent report, the global average cost of a breach reached $4.44 million. Moreover, the Verizon Report found ransomware present in 44% of all SMB breaches.
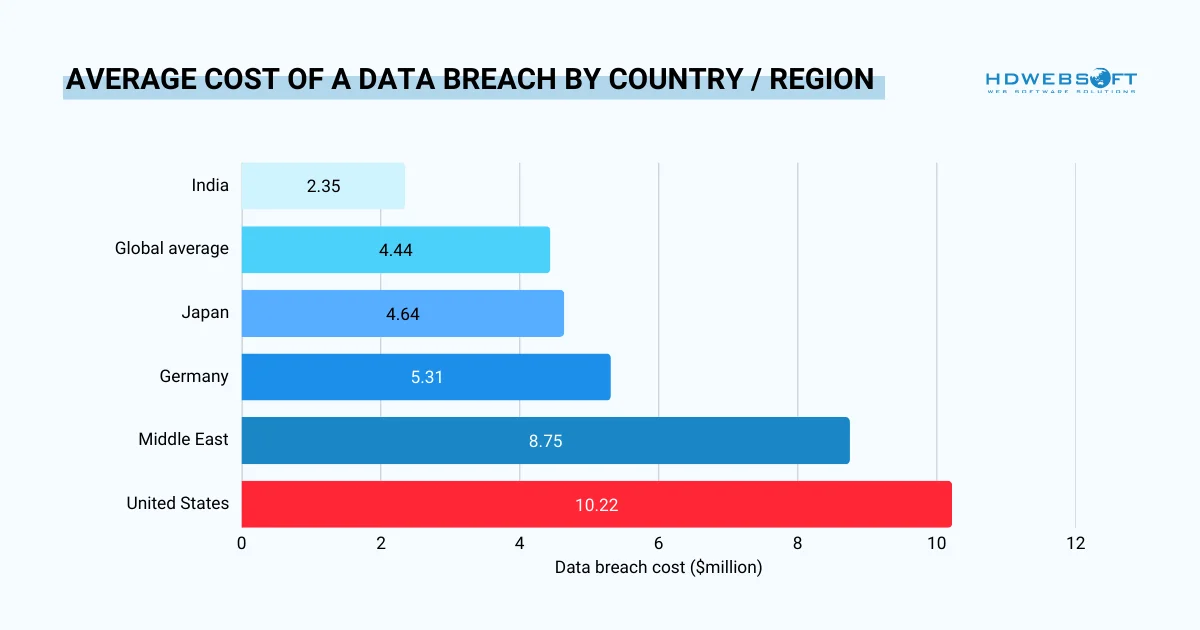
U.S. organizations face more than double the global average
This guide covers everything your organization needs to know: what managing data security truly means, why the CIA Triad underpins it, the most dangerous threats to defend against, and how to build a program that actually holds up.
- 1) What Is Data Security Management?
- 2) The CIA Triad: Foundation of Data Security
- 3) Common Data Security Threats and Vulnerabilities
- 4) Core Components of a Data Security Management System
- 5) How to Implement Data Security Management
- 6) Data Security Management Frameworks and Tools
- 7) Frequently Asked Questions
- 8) Final Thought
What Is Data Security Management?
At its core, data security management is the organized practice of protecting sensitive information from unauthorized access, corruption, theft, and loss, throughout its entire lifecycle. It combines policies, technologies, and human processes into a coherent, ongoing program rather than a series of one-off measures.
Crucially, it is different from general IT security. General IT security protects infrastructure, for example, networks, devices, and systems. Managing data security, however, is data-centric. Its focus starts at the data asset itself: where it lives, who touches it, how it moves, and when it should be deleted.
Organizations typically formalize this through a secure data management system. It’s a structured framework of controls and governance that brings consistency across teams, locations, and data environments.
Three pillars hold up every effective program:
- People: training, accountability, and a security-first culture
- Process: documented policies, access protocols, and incident response plans
- Technology: tools that enforce, monitor, and automate controls
The CIA Triad: Foundation of Data Security
Every cyberattack, without exception, targets at least one of three core principles. Data security management teams use this framework to evaluate vulnerabilities and design defenses. Thus, understanding these principles is essential before choosing tools or writing policies.
Confidentiality
Only authorized people and processes should access or modify sensitive data. This principle drives access controls, encryption, and the least-privilege model.
Integrity
Data must remain accurate, trustworthy, and free from unauthorized alteration. For instance, audit logs, checksums, and change management all serve this principle.
Availability
Sensitive data must be accessible to those who need it, when they need it. For example, DDoS defenses, redundancy planning, and backup strategies protect this pillar.
Every component, control, and best practice covered in this guide maps back to protecting one or more of these three principles. When evaluating any new threat or tool, ask: which pillar does it affect?
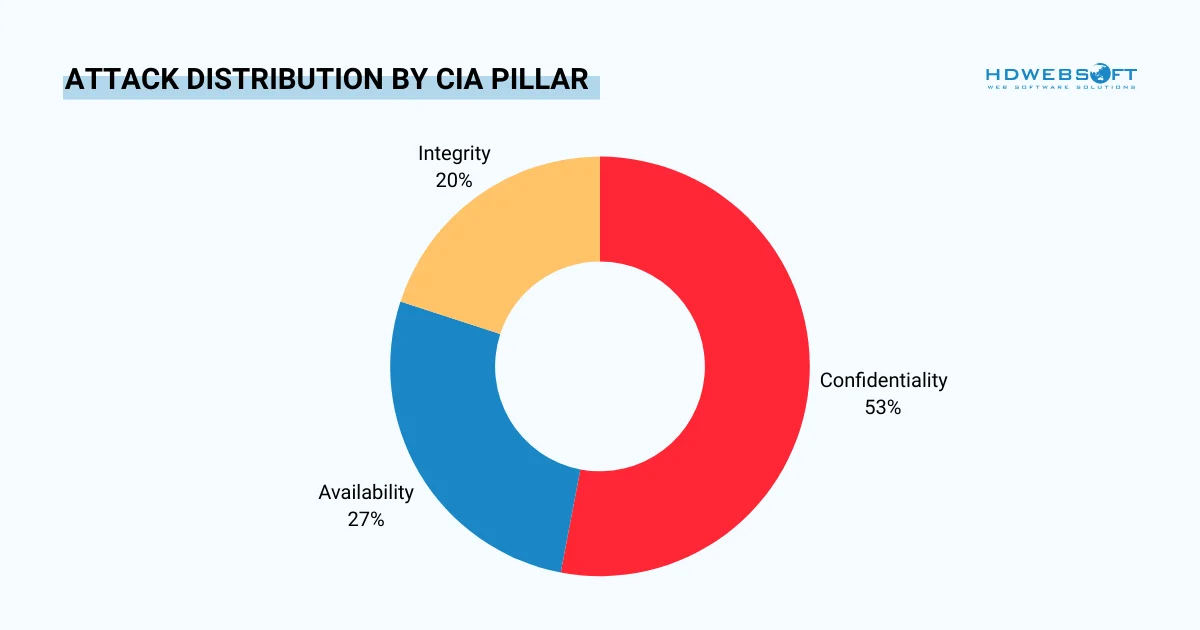
Which principle do threat actors target most frequently?
Common Data Security Threats and Vulnerabilities
Understanding the threat landscape is a prerequisite for designing effective defenses. Threats fall into two broad categories, external and internal, and the 2025 data security management statistics shows both are escalating.
External Threats
The external actors drive the majority of breaches. However, their tactics are evolving rapidly. According to the Verizon report, vulnerability exploitation jumped 34% year-over-year, and third-party involvement in breaches doubled from 15% to 30% in a single year.
| Threat Type | How It Works | CIA Pillar Targeted | 2025 Prevalence |
| Ransomware | Encrypts files and demands payment for access | Availability, Confidentiality | 44% of breaches |
| Phishing / Social Engineering | Tricks users into revealing credentials or taking harmful actions | Confidentiality | 16% as initial vector |
| Stolen Credentials | Reuses or buys compromised login data | Confidentiality | 32% of all attacks |
| Zero-Day Exploits | Targets vulnerabilities before a patch exists | All three | +34% YoY |
| DDoS Attacks | Floods systems to deny access to legitimate users | Availability | 13% of initial vectors |
| Supply Chain Attacks | Exploits vulnerabilities in third-party vendors | All three | 30% of breaches |
Internal Threats
On the other hand, data security management internal risks are often underestimated, and yet, they are among the costliest to remediate. As a matter of fact, the human element remains a factor in 60% of all breaches.
Malicious Insiders
Employees, contractors, or vendors with legitimate access can misuse it deliberately. Insider threats cost organizations a staggering $17.4 million annually per business in 2025. Their deep knowledge of internal systems, access credentials, data locations, security blind spots, makes detection exceptionally difficult. Unlike external attackers, malicious insiders don’t need to break through perimeter defenses as they are already inside.
Moreover, detection relies heavily on behavioral monitoring. Unusual login times, bulk data downloads, or access to systems outside someone’s normal job scope are all indicators worth flagging. Hence, User and Entity Behavior Analytics (UEBA) tools are specifically designed to surface these anomalies before they escalate.
Negligence and Human Error
Not all data security management internal threats are intentional. Misconfigured systems, reused passwords, careless data sharing, and accidental exposure through misdirected emails can be just as damaging as a targeted attack. A well-meaning employee who emails a sensitive spreadsheet to the wrong recipient, or an IT admin who leaves a cloud storage bucket publicly accessible, can trigger consequences equivalent to a deliberate breach.
In addition, reducing negligence-driven incidents requires two parallel efforts. First, technical controls, DLP tools, email warning prompts, and access restrictions, create friction that catches mistakes before they cause damage. Second, a strong security culture normalizes careful data handling as a daily habit, not just a compliance requirement.
Shadow AI
Emerging in 2025 as a distinct insider risk category, shadow AI refers to employees using unsanctioned AI tools without IT oversight or approval. For example, they include public chatbots, AI writing assistants, and code generation tools. Without proper data security management, organizations have little visibility into how sensitive information is shared or processed through these tools.
The risk is not the tools themselves, but what gets fed into them. Employees routinely paste customer data, internal financials, source code, or legal documents into these platforms. They do it without considering that inputs may be used to train models or stored on third-party servers.
According to IBM, shadow AI was a contributing factor in 20% of all breaches studied, adding an average of $670,000 to the total breach cost.
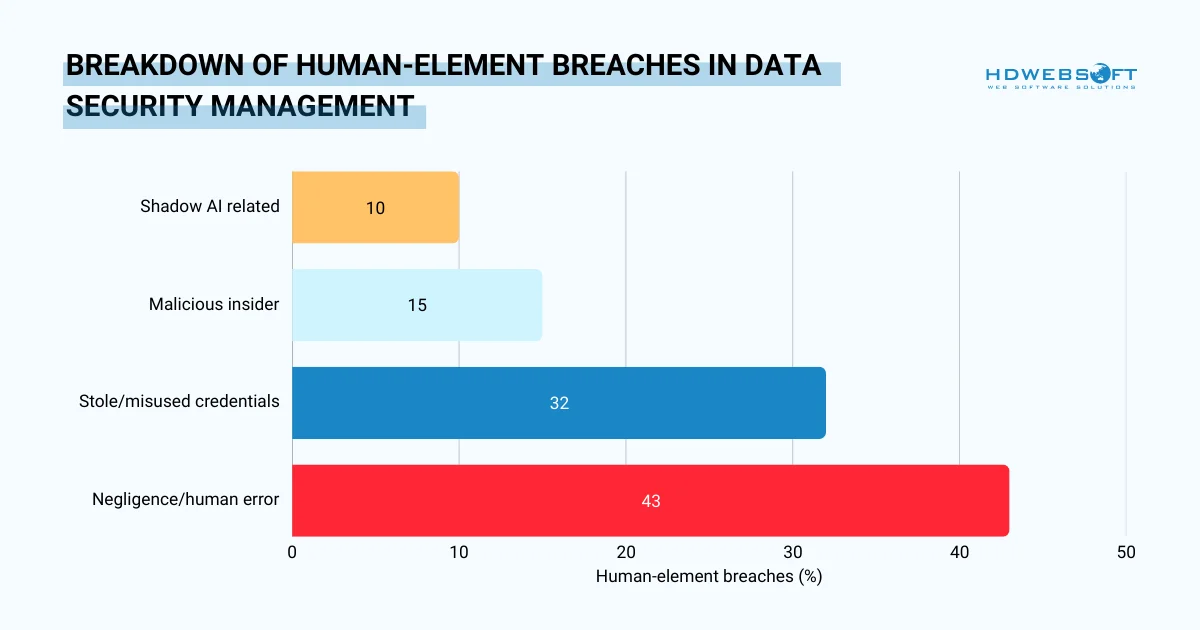
The 60% of breaches in a data security management system involving people, by sub-category
Core Components of a Data Security Management System
A robust data security management system is not a single product. Rather, it is a layered combination of technical controls and governance processes where each addressing a distinct exposure point. Skipping any one layer creates gaps that attackers actively look for.
Data Discovery and Classification
Before any control can be applied, organizations must know what data they hold and where it lives. Discovery involves systematically inventorying data assets across on-premises systems, SaaS platforms, databases, and endpoints. Without this step, sensitive information can exist in forgotten file shares or shadow IT systems, completely outside any protection.
Classification follows discovery. It assigns each data asset a sensitivity tier, typically public, internal, confidential, and restricted, based on the harm its exposure would cause. Moreover, classification drives every downstream decision: who can access the data, how it must be encrypted, how long it should be retained, and how quickly a breach involving it must be reported.
Data Governance and Retention
Classification in a data security management system alone is not enough. Organizations also need a governance layer. Namely, policies governing who owns each data type, who can approve access requests, and how long data should be retained.
Hence, retaining data beyond its useful life increases exposure for no benefit. Per the IAPP, the principle of data minimization holds that organizations should keep personal information only as long as necessary to fulfill its stated purpose.
Access Control and Identity Management
Unauthorized access is the most common root cause of data breaches. Stolen or misused credentials account for 32% of all attacks. Therefore, a strong access control layer directly addresses this.
The cornerstone principle is least privilege: users should only access the data and systems their specific role requires, nothing more. This is because over-permissioned accounts are a silent risk. When an employee’s credentials are compromised, least privilege limits the blast radius of the attack.
Role-Based Access Control (RBAC)
RBAC in a data security management system ties access permissions to job functions rather than individual users. When roles change, either through promotions, transfers, or departures, access can be updated or revoked in a single action. That’s why regular access reviews, at least quarterly, should verify that permissions still match current responsibilities.
Multi-Factor Authentication (MFA) and SSO
Passwords alone are insufficient. MFA requires a second verification step, making credential theft far less useful to attackers. Pairing MFA with single sign-on (SSO) reduces password fatigue while centralizing authentication management. According to CISA, MFA can block over 99% of automated account compromise attacks.
Encryption
Encryption transforms readable data into ciphertext that is unusable without the correct decryption key. Even if an attacker bypasses access controls, encrypted data remains worthless to them. This makes encryption a last line of defense and a non-negotiable element of any data security management system policy.
There are two coverage areas that matter most. Encryption at rest protects stored data, databases, file systems, and backups, using standards like AES-256. Meanwhile, encryption in transit protects data moving across networks, typically via TLS 1.2 or higher. Both must be in place; securing only one leaves the other as an easy target.
Key Management
In fact, encryption is only as strong as how well encryption keys are protected. Poor key management, storing keys alongside the data they encrypt, or failing to rotate keys regularly, undermines the entire control. Hence, organizations should use dedicated key management services (KMS), rotate keys on a defined schedule, and audit key access logs.
Data Loss Prevention (DLP)
DLP tools monitor data movement across endpoints, email, web channels, and SaaS applications. They detect when sensitive data is being copied, uploaded, or emailed outside authorized channels. The best thing is, these data security management tools can block the transfer in real time.
The rise of shadow AI has made DLP more urgent. Employees pasting confidential data into public AI tools is now one of the fastest-growing exfiltration vectors. Additionally, DLP policies can be configured to flag or block these transfers automatically, closing a gap that perimeter security tools cannot address.
Monitoring, Logging, and Incident Response
Continuous monitoring is what separates reactive organizations from resilient ones. Without it, breaches go undetected for weeks or months, costing far more in the end. Thus, organizations with mature monitoring capabilities cut that window significantly.
Furthermore, centralized logging through a SIEM (Security Information and Event Management) platform aggregates activity data from across the environment. Machine learning-based anomaly detection can surface subtle pattern changes, unusual login times, unexpected large data exports, that rule-based systems miss.
Incident Response Planning
Monitoring in a data security management system catches threats; incident response contains them. Every organization needs a documented response plan before an incident occurs, not after.
The plan should define clear escalation paths, assign roles, and specify notification timelines required by GDPR, HIPAA, or other regulations. Plus, regular tabletop exercises test the plan against realistic scenarios.
Backup and Recovery
Reliable backups are the ultimate safety net, particularly against ransomware, which is now present in 44% of all breaches. Without tested backups, an organization facing ransomware faces a binary choice: pay the ransom or lose the data. Neither outcome is acceptable.
For your information, effective backup strategy follows the 3-2-1 rule: maintain three copies of data, across two different media types, with one copy stored offsite or offline.
Critically, backups must be tested. A backup that has never been restored is not a backup; it is an untested assumption. Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO) should be defined and validated during regular drills.
How to Implement Data Security Management
Standing up a data security management program requires more than deploying tools. It demands a structured, phased approach. One that builds policy before technology, and governance before automation.
The steps below reflect managed data security best practices validated across NIST, ISO 27001, and the CIS Controls.
1. Conduct a Data Audit
Classify what you have before applying any controls. For example, identify sensitive assets, where they live, and who currently has access.
2. Establish a Formal Policy
Document your data security management system policy, then get executive sign-off and communicate it across the organization.
3. Adopt a Recognized Framework
Use NIST CSF, ISO/IEC 27001, or CIS Controls as your structural backbone. This is because these frameworks provide a proven, auditable starting point.
4. Enforce Least Privilege & Access Controls
Implement RBAC, MFA, and SSO across all systems. Regularly review and revoke unnecessary access permissions.
5. Train Employees Continuously
One-off onboarding sessions are insufficient. Hence, it’s important to build a culture of ongoing security awareness.
6. Run a Cyclical Risk Management Process
Identify risks → Assess & evaluate → Implement controls → Monitor → Repeat. Risk management is never a finished task.
7. Test and Audit Regularly
Penetration tests, vulnerability assessments, and internal audits keep the program current.
On Managed Data Security
Organizations that lack in-house expertise often turn to managed data securityproviders (MSSPs). These services handle monitoring, threat detection, and incident response externally. The trade-off is cost versus control — but for lean security teams, a managed model can dramatically reduce mean time to contain a breach.
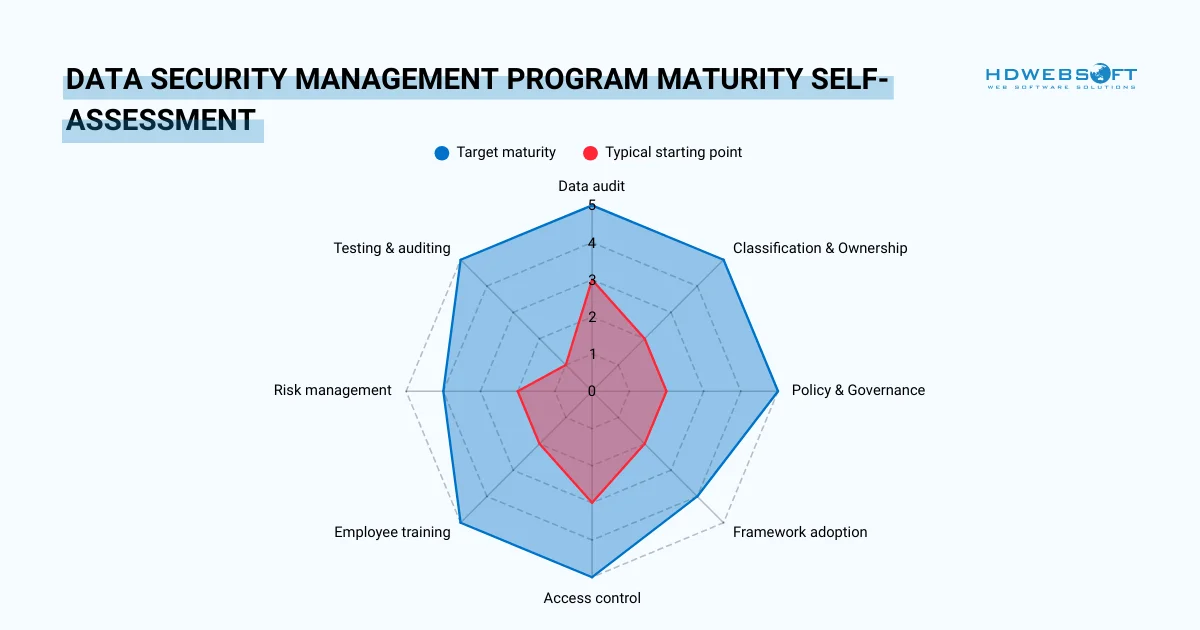
How a typical starting data security management services point compares to target maturity across all eight implementation areas
Data Security Management Frameworks and Tools
Choosing the right frameworks and tools gives your managed data security program structure and scale. Frameworks provide the “what and why” — tools handle the “how.”
Security Frameworks
Three frameworks consistently form the backbone of enterprise data security management programs. They are complementary, not competing.
| Framework | Best For | Key Strength |
| NIST CSF | All organizations | Maps to five core functions: Identify, Protect, Detect, Respond, Recover |
| ISO/IEC 27001 | Enterprises seeking international certification | Globally recognized; provides auditable evidence of a formal ISMS |
| CIS Controls | SMBs and teams with limited resources | Prioritized, actionable controls ranked by impact |
Tools by Category
Technology supports your program; however, it does not replace policy or training. Hence, deploying tools strategically across these categories is a necessary:
Detection & Response
SIEM platforms such as Splunk and Microsoft Sentinel provide centralized logging and real-time alerting. Remember to pair them with endpoint detection and response (EDR) tools for broad coverage across devices.
Access & Identity
IAM platforms like Okta or Azure AD enforce access control policies at scale. They also provide the audit trails required by HIPAA and GDPR. Password managers and phishing-resistant passkeys further reduce credential risk.
Data Protection
DLP in data security management system solutions prevent unauthorized data movement across endpoints, email, and web channels. Encryption tools secure data at rest and in transit. Together, these controls directly address Confidentiality – the first pillar of the CIA Triad.
Frequently Asked Questions
What is data security management?
Data security management refers to the process of protecting data from unauthorized access, breaches, and loss using tools such as encryption, access control, monitoring systems, and security policies.
What is the cost of ignoring data security management?
The cost includes financial losses, downtime, regulatory fines, customer churn, and long-term reputation damage. These costs often exceed the investment required for proper security systems.
Why is data security important for businesses?
Data security ensures business continuity, protects customer trust, and prevents financial and legal risks. In modern digital environments, it is critical for maintaining competitive advantage.
How can companies improve data security management?
Companies can improve security by adopting proactive strategies such as continuous monitoring, AI-based threat detection, cloud security solutions, and regular system audits.
Final Thought
Managed data security is not a project with an end date. It is a continuous program that evolves alongside threats, technology, and regulatory expectations. The organizations that treat it as foundational, not reactive, are the ones that contain breaches faster, pay less when incidents occur, and retain customer trust long-term.
The cost of inaction
IBM’s 2025 report found that organizations using AI and automation extensively in security saved an average of $1.9 million per breach compared to those that didn’t. The investment in a structured data security management program pays for itself many times over.
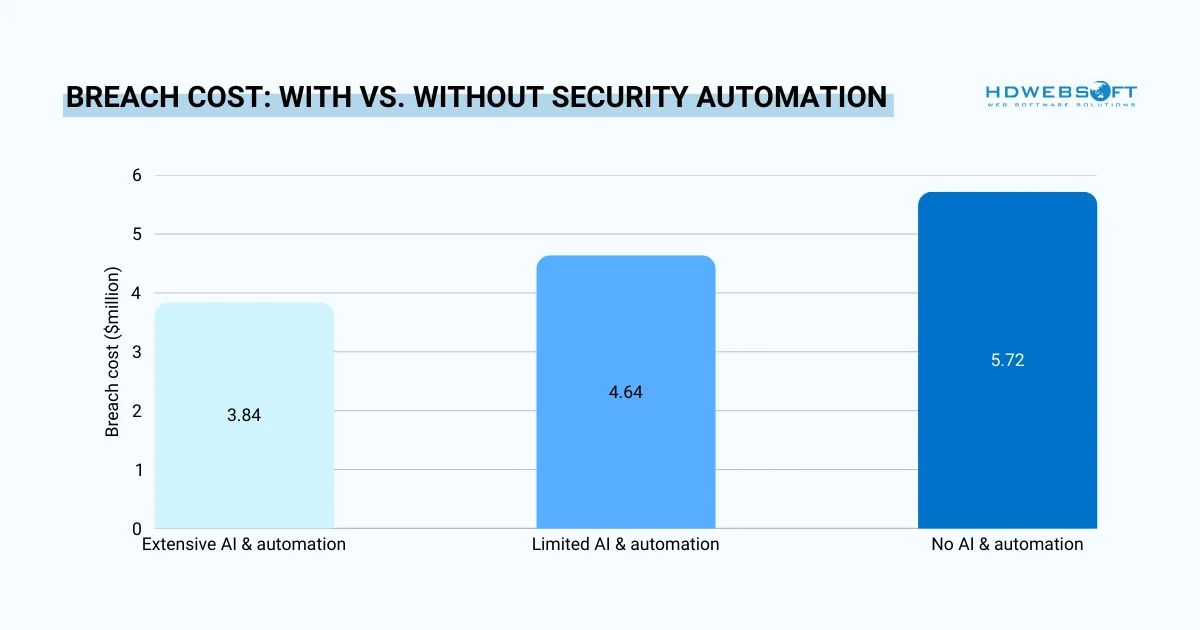
Organizations using AI & automation in security spend significantly less per breach
Start with a data audit. Build your policy. Choose a framework. Train your people. Then iterate. Because the threat landscape never stops changing, and neither should your defenses. Partnering with a trusted cybersecurity services provider like HDWEBSOFT can help organizations implement and maintain effective data security strategies at every stage.